IP Reputation for Proxies: Do they matter and what to look for?
When you use a proxy, you are practically borrowing an IP address to mask your original one. But what if the IP has a bad history? Websites constantly evaluate the trustworthiness of incoming traffic. Hence, the reputation of the IP address behind your connection always matters. If you are wondering about IP reputation for proxies, this guide answers all your questions.
What is IP Reputation?
IP reputation is essentially a trust score assigned to an IP address based on its historical behavior. This score is used by websites, email servers, and security systems to assess the trustworthiness of an IP address. However, there isn’t one global IP reputation score. Each provider maintains its own signals and thresholds. Similarly, some rely on centralized scoring systems, such as Cloudflare, DataDome, or IPQualityScore, to evaluate risk.
An IP address with a high score is considered legitimate and granted access freely. Alternatively, an IP with a low score raises red flags. It could even lead to immediate request blocks, CAPTCHA challenges, rate limits, security reviews, and additional hassles.
What Damages a Proxy IP’s Reputation?
It is important to understand the factors that damage a proxy IP’s reputation. So you can avoid them by choosing a high-quality proxy service.
Note that not every blacklist is relevant for proxy usage. Many reputable databases focus almost entirely on email-sending behavior rather than on general web activity. Email-focused lists maintained by organizations often track IPs that send spam or bulk email. Similarly, many other services focus heavily on email reputation.
That said, these lists are not particularly important for proxying. Most reputable proxy providers block common email ports, especially SMTP port 25, as it is often used for sending an email. Therefore, email reputation doesn't always matter.
Yet, some factors still affect proxy IP reputation and can lead to blocks or restrictions. That might include:
- Spam, Abuse, Reports: Let’s say an IP address appears in abuse databases linked to bot traffic, scraping abuse, or credential stuffing. Websites will treat their requests with heightened suspicion.
- Shared Subnets, Bad Neighbors, and Recycled IPs: Activity from IPs in the same subnet and recycled IPs also carry negative history, especially if previous users generated abuse signals.
- Open Proxies, Malware Traffic, and Sudden Request Spikes: Public proxies can attract spam bots, brute-force attempts, and malware. All these factors damage trust quickly.
The way a proxy network is sourced is also quite important. Providers that focus on ethical proxy sourcing typically maintain cleaner IP pools. This reduces the risk of recycled or abused addresses.
How IP Reputation Affects Common Proxy Use Cases
The theoretical importance of IP reputation becomes very real when you apply it to common proxy use cases. In almost every scenario, the quality of your IP address is a deciding factor between success and failure. A low-reputation IP can sabotage your efforts before you even begin, which results in frustrating blocks and inaccurate results.
Here’s how a low IP reputation score can affect common proxy uses:
Web Scraping and Anti-bot Systems
Web scraping involves collecting large amounts of data from the web, which is protected by sophisticated anti-bot systems. These systems are designed to distinguish between human visitors and bots. The first thing they look for is the incoming IP's reputation.
Therefore, you will face immediate resistance if you attempt to scrape a site using a proxy with a poor IP reputation.
Ad Verification and QA Testing
Ad verification ensures that digital advertisements are displayed correctly to the intended audience and do not hint at any inappropriate content. Many websites and applications use QA (Quality Assurance) testing to simulate user experiences across different geographic locations.
Both ad verification and QA testing require a clean, unbiased view of the web. So websites and ad networks might treat you as a suspicious user if you use a proxy with a bad IP reputation.
Multi-Account, eCommerce, and Social Sessions
Managing multiple accounts on platforms like Amazon, eBay, Facebook, and Instagram is difficult. It requires each account to appear as a distinct and legitimate user. These platforms have strict rules against operating multiple accounts and use advanced systems to detect them.
If one account is associated with a blacklisted IP, the platform may automatically flag and suspend all other accounts that have used the same IP.
How To Check Proxy IP Reputation Before Deployment?
You should first verify the quality of an IP before investing in a proxy service. Fortunately, several techniques are available to verify a proxy's IP reputation.
It is always a good idea to be proactive about the verification process, as it may help you avoid issues later on. A variety of online services specialize in tracking and reporting on IP reputation proxies. A combined usage of these tools will give you a more complete picture of an IP’s standing. Here are some examples:
Blacklist Checkers
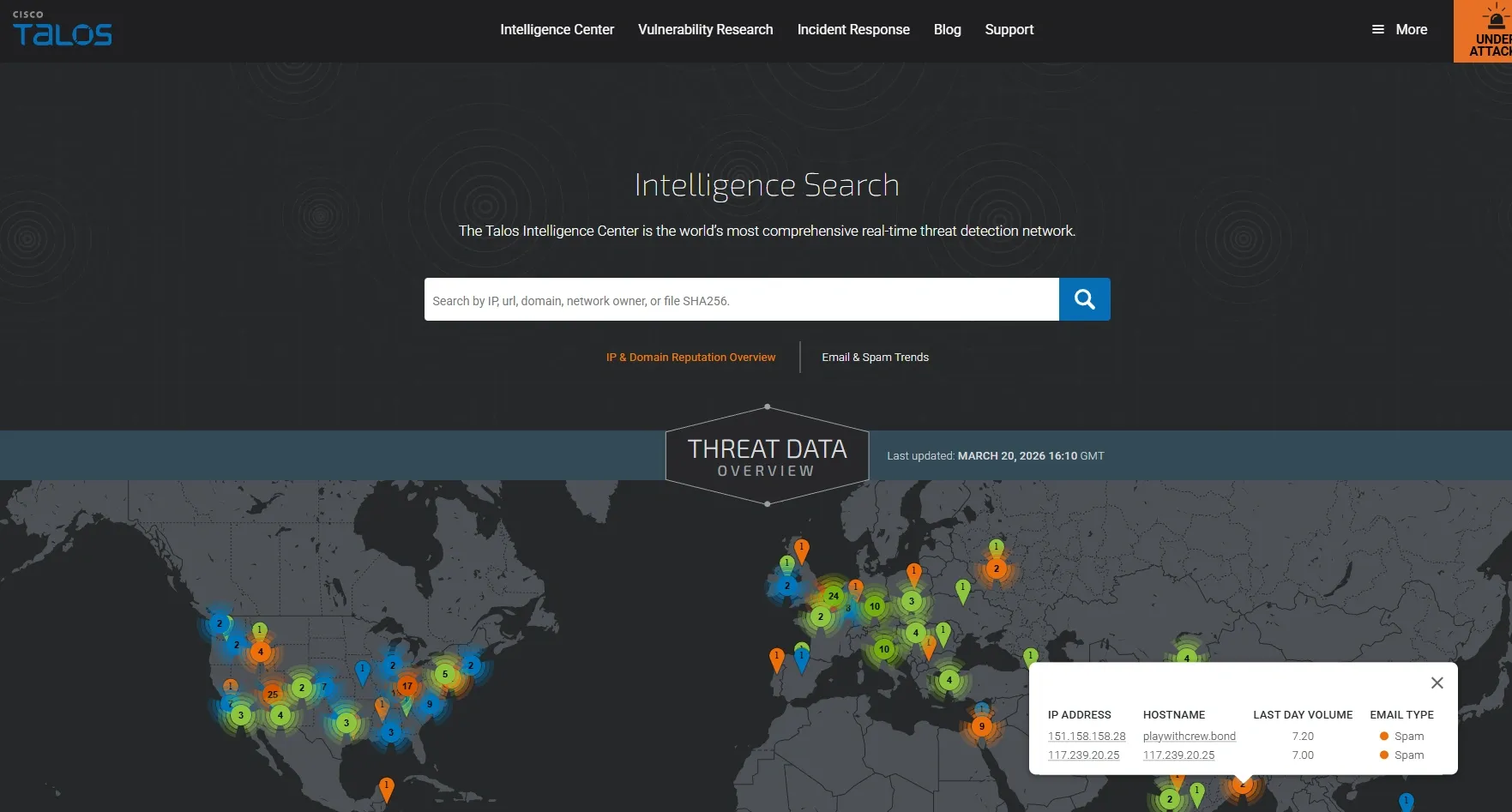
The most crucial check is to verify whether an IP is listed on any major DNS-based blacklists (DNSBLs). These lists are used to flag IPs linked to spam or abuse. Tools like CISCO Talos can scan an IP across multiple blocklists. They can also provide a quick overview of any issues.
Reputation Block List (BRBL)
These are widely used by email providers and network administrators. An appearance on one of these lists is a major problem. Services maintained by Spamhaus are among the most commonly referenced in this category.
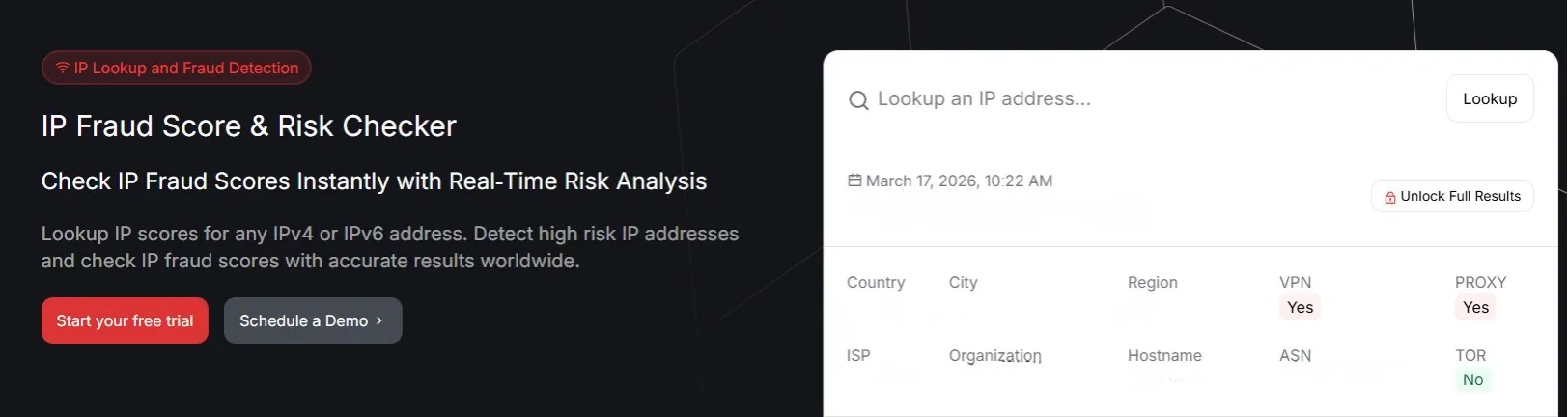
Fraud and Abuse Score Tools
These services offer a more nuanced IP reputation check. They verify an IP's recent history to see if there are any signs of fraud or bot activity. They then give it a score from 0 to 100. Some common examples are IPQualityScore, Scamalytics, IPData, and IP2Location.
What Makes a Proxy IP Trustworthy?
A deeper analysis of an IP’s attributes is essential beyond a simple pass/fail. These factors can tell quite a lot about its quality.
- ASN Autonomous System Number: The ASN is a number that identifies which network an IP address belongs to. If it is from a well-known hosting provider such as Amazon or Google Cloud, it is a data center IP address. If it is from a consumer ISP such as Comcast or Verizon, it is a residential IP address. Make sure the ASN matches the type of proxy you are paying for.
- Geolocation: Verify that the country, city, and ISP match what your provider said you should expect. Errors or inconsistencies across different geolocation databases are a red flag. However, geo-targeting is a sophisticated function that lets you target IPs by country, region, or even city.
- Usage Type Classification: This is a critical concept. IP intelligence databases often classify IPs into "Usage Types," such as Datacenter, Commercial, ISP, or Mobile. For most sensitive use cases, you want IPs classified as ISP or Mobile, as these are associated with real consumer devices and carry the highest level of trust.
Choosing Proxy Types and Does it Really Matter?
The type of proxy you choose is one of the most important decisions you will face. While IP reputation matters, it can be a misleading metric on its own.
Let’s look at how different proxy types affect performance across common use cases.
Datacenter Proxies
These are the most common and affordable. The IPs are owned by data centers, not residential ISPs, making them easier to detect via their ASNs. They are fast but more likely to be blocked on strict websites. Therefore, they are ideal for less-sensitive tasks.
Residential Proxies
These proxies use IPs assigned by ISPs to real users, so traffic appears more natural to websites. This makes them effective for scraping, account management, and e-commerce. That is why our residential proxies are ethically sourced and maintained for high performance.
A 2020 study shows that only 0.27% of the residential proxies were associated with verified attacks, though this may not fully reflect current conditions, as detection systems have evolved.
Mobile Proxies
These proxies use IPs from mobile carriers and are considered highly trustworthy due to their dynamic nature. They often operate behind carrier-grade NAT, meaning thousands of users share a single IP address. Mobile proxies are much harder for platforms to ban because blocking one IP can affect many real users. However, they are more expensive and typically used for tasks that require the highest level of trust.
Dedicated vs Shared IPs
A dedicated IP is assigned exclusively to you. You have full control over its activity and its real-world performance. So, if you use it cleanly on your target sites, it will remain effective. This is a great option for managing a few high-value accounts where consistency matters most.
On the other hand, a shared IP is used by multiple users. This makes them cheaper but also involves risk. If another user gets the IP blocked on your target site, it affects your performance. A good provider mitigates this by vetting users and monitoring for abuse. But the risk still exists.
Sticky Sessions vs. Rotation: Which One Helps?
Sticky sessions are a feature that keeps the same proxy IP for an extended period. That might range from minutes to several hours. Sticky sessions are good for tasks that require a consistent identity. That might include multi-step checkout processes or continuous login on an account.
Rotating proxies automatically assign a new IP address for every request or after a fixed time. This is suitable for large-scale web scraping as it helps avoid rate limits by distributing your requests across many IPs.
However, rotation is not a substitute for a high-quality pool. If the rotating IPs are already blocked by your target, you will still experience a high failure rate.
How to Protect Reputation Across a Proxy Pool
Choosing a provider with a high-quality proxy pool is the first step. The second is using those proxies responsibly to maintain their reputation.
These are some good practices to help you achieve a high success rate and maintain a clean proxy pool.
- Control your request rate: Don’t flood servers with requests by controlling the speed of your requests.
- Request quality: Keep requests clean and consistent. Occasional errors like 404s can occur during normal browsing (e.g., due to broken or moved pages). But repeated issues such as frequent 403 responses may signal bot-like activity and raise suspicion.
- Differentiate workloads by risk level: Use a set of proxies for high-risk tasks, such as aggressive scraping, and another set for lower-risk tasks, such as account maintenance, to preserve your best IPs.
- Ban detection and CAPTCHA usage: Monitor for errors and codes that may indicate IP bans. Another good practice is to monitor the proxy network itself, which will help you avoid unexpected outages. Keep in mind that outages aren’t related to IP reputation. They are infrastructure issues and don't mean your IPs are untrustworthy. Many proxy services, like ours, maintain a status page where users can quickly check whether any of our services are experiencing outages.
- Prioritize stability: This is a significant aspect that will help ensure IP trust. A robust infrastructure, such as networks optimized for 99.9% uptime, will ensure a better, smoother user experience.
Proxy Pitfalls that Quietly Burn IP Trust
Some common mistakes can quickly damage your proxy's reputation. Such pitfalls, though minor, can have a significant impact on your success.
Too Many Requests with a Non-Human Traffic Pattern
This is arguably the most common reason why proxy IPs get banned. Automated scripts often execute tasks with machine-like precision and speed. Some common giveaways are:
- Making requests every 1.5 seconds on the dot
- Accessing a site in the exact same sequence every time
- Making requests on multiple pages in a few seconds
Human behavior is random. Thus, your automation must mimic this randomness to protect your IPs. Introduce variable delays, keep request rates within believable limits, and randomize your navigation paths.
Using Public or Open Proxies
Free public proxies are widely available online, but they are mostly a trap. They are slow and unreliable, and their IPs have the worst possible reputation due to relentless abuse by spammers and hackers worldwide.
Moreover, a public proxy for any serious task is a guaranteed way to fail. It can also expose you to security risks as the proxy operator can see all of your traffic.
Browser Fingerprint
Your IP address is only one aspect of your online identity. Websites also track your browser fingerprint, which includes dozens of identifying characteristics. That might be your User Agent string, screen resolution, installed fonts, browser plugins, and more.
If you are using a pristine residential IP but your browser fingerprint is inconsistent or flags you as a bot (e.g., using an outdated User Agent), you will still get blocked. Effective proxy usage must be paired with careful fingerprint management.
A Simple Pass/Fail Checklist for Proxy Buyers
Here is a quick checklist you can use to test a proxy IP buyer:
- Usage Type: Are you paying for residential proxies, but the IP is classified as "Datacenter" by IPInfo or IP2Location? (If yes, FAIL)
- ASN Check: Does the ASN belong to a hosting/server company instead of a consumer ISP? (If yes, likely a FAIL for residential use cases)
- Abuse Score: Does the IP have a high fraud or abuse score (e.g., >75 on IPQS)? (If yes, FAIL)
- Geolocation: Is the country completely different from what was advertised? (If yes, FAIL)
